You really shouldn't wait.
Getting started isn't hard to do.
Good security isn't complicated — but it does need to be intentional. With a password manager, MFA, and basic email protections in place, you eliminate the easiest attacks on small businesses.
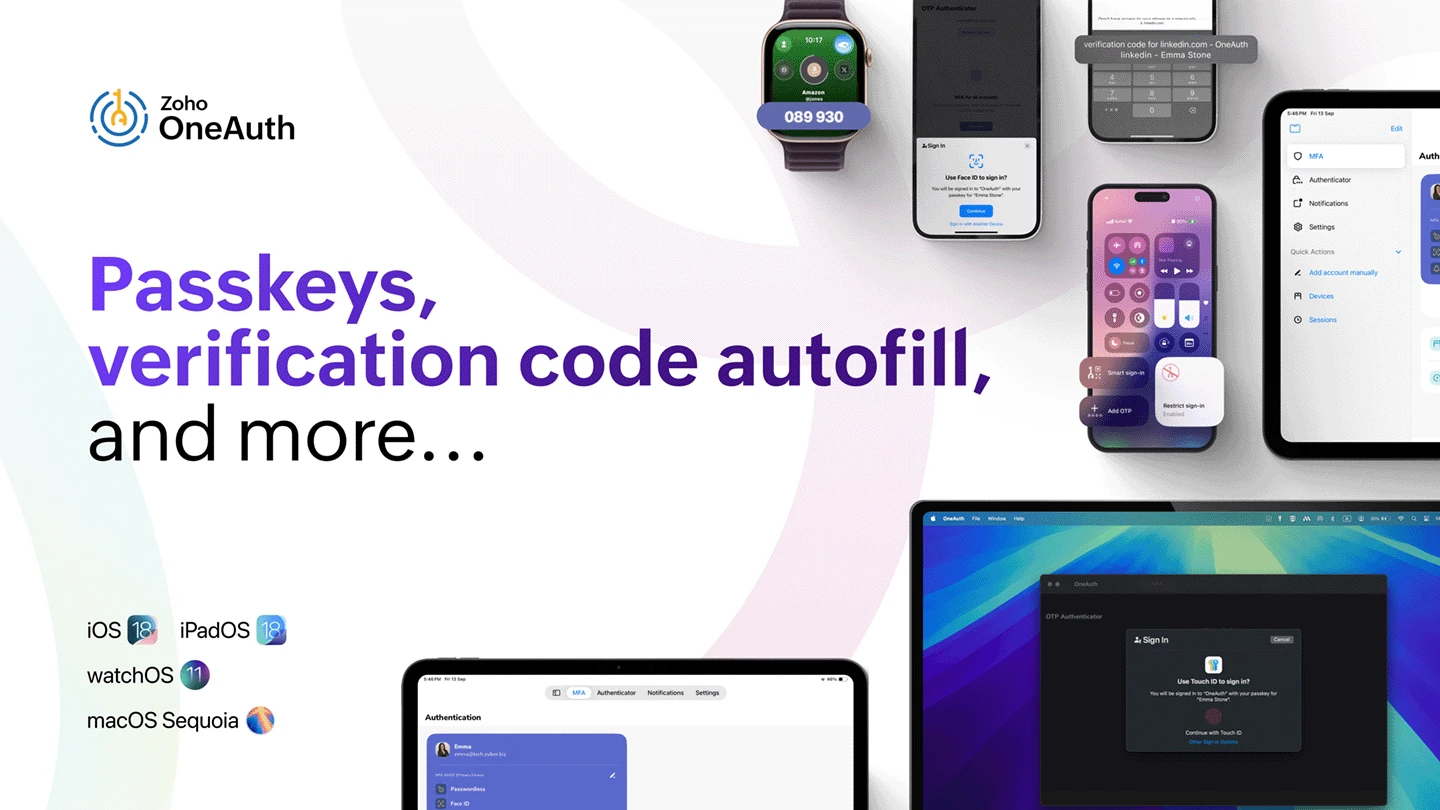
The good news? Zoho Vault and OneAuth already do most of the work for you.
If you're not already worried, let us scare you more.
Schedule a Free Consultation